QAlista
Interaction Intelligence
Customer signals are everywhere.
We help you
listen, understand and adapt
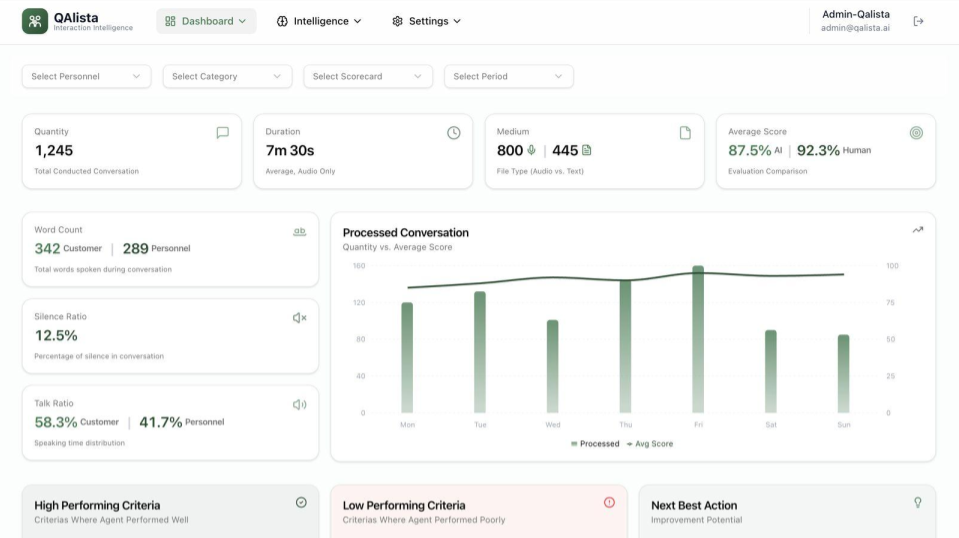
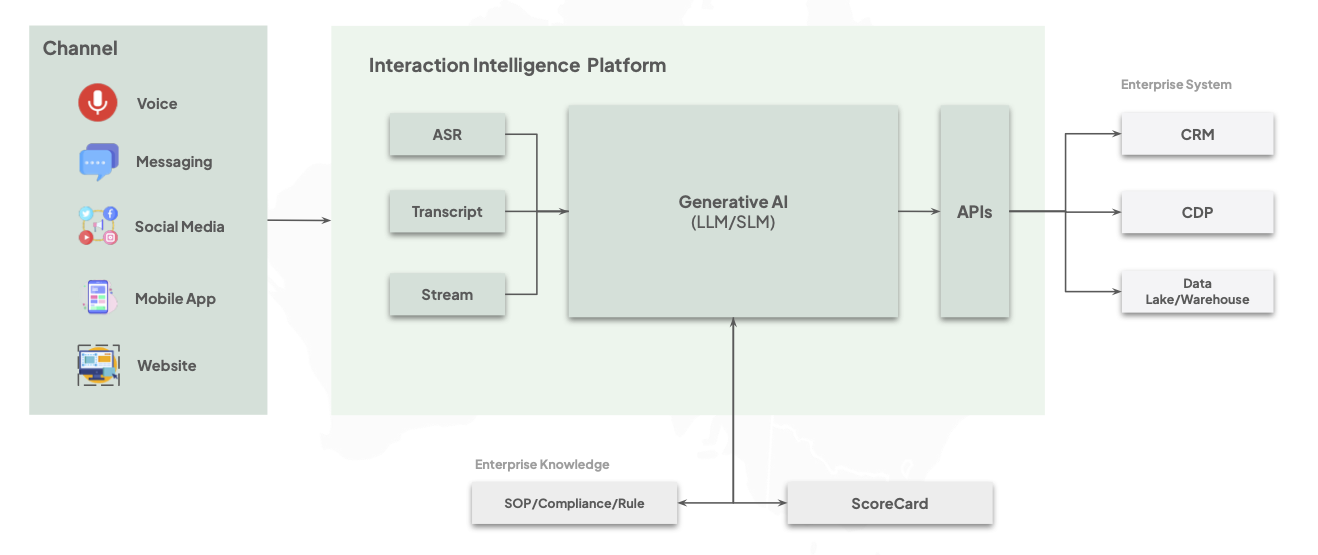
QAlista identifies implicit customer interactions across every channel, delivering the surgical precision of human analysis with the infinite scale and speed of Generative AI.
Human Can't Scale
Traditional human-based analysis is plagued by high costs, subjective bias, and extreme sampling limitations that leave 95% of your customer interactions unmonitored.
Human Capacity Constraint
Operational Inconsistency
Manual analysis is plagued by high costs and extreme sampling limitations.
- •Delayed DetectionWeekly review cycles skip real-time signals.
- •Subjective BiasCompliance rules applied inconsistently.
- •Sampling GapRandom sampling misses 95% of total volume.
Financial & Retention Leakage
Undetected errors and missed opportunities directly impact the bottom line.
- •Missed RevenueUSD 15M missed monthly in opportunities.
- •Invisible ChurnAcquisition costs 5x-25x higher than retention.
- •Hidden ViolationsCompliance errors remain unknown.
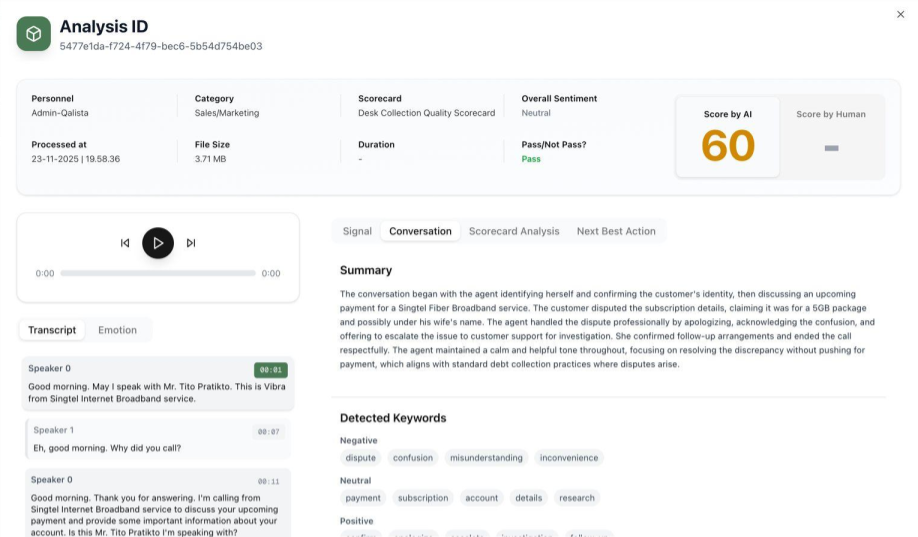
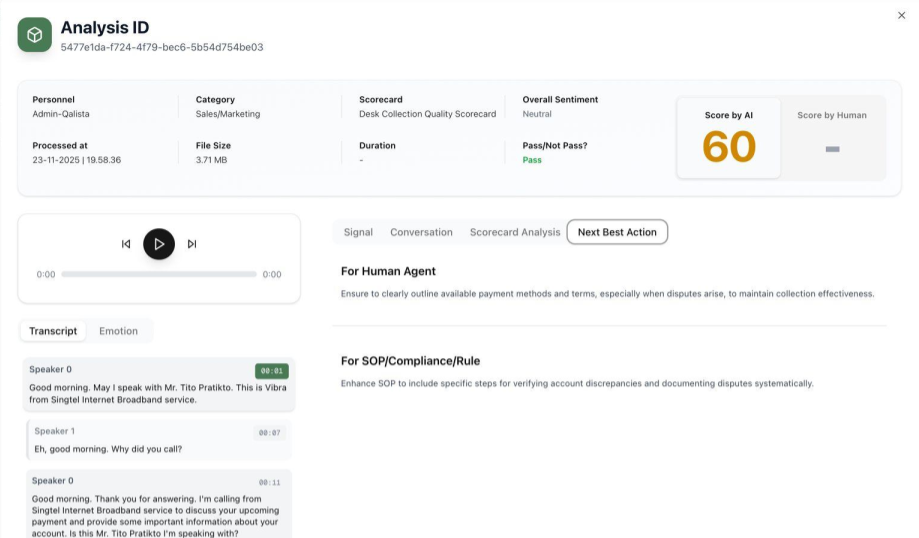
AI Agent for Interaction Intelligence
Voice/Text Source
Accommodate Voice and Text data source seamlessly.
Dynamic Scorecard
Formulate your own Scorecard with custom logic.
Human-in-The-Loop
Involve Human experts as part of checking procedure.
On-Premise Ready
Ensure maximum data security & sovereignty.
Dynamic LLM
Proprietary fine-tuned or Bring Your Own (BYO).
Next-Action Engine
Create scorecards using our dynamic prompt engine.
3rd Party Integration
Built-in API Gateway for seamless interoperability.
AI Agent-Driven
QAlista utilizes a proprietary multi-agent framework to process, transcribe, and reason through interactions in advanced, providing deep forensic insights with machine-level consistency.
Delivered Performance
Partners
Strategic Alliance
Compliance
Adopted Standard





Voice of Customer
Discover how industry leaders across Asia Pacific are transforming their customer operations and driving measurable growth with QAlista.
Commercial Model
Simple. Scalable.
Transparent.
On-Premise InfrastructureOn-Premise and Private Cloud deployments available for high-security sectors (Banking, Gov) requiring full data sovereignty and air-gapped environments.
Volume TieringEnterprise-grade discounts are available by request for high-volume accounts.
Customer Success ProgramIncludes 24/7 technical monitoring, tiered SLA commitment, and dedicated prompt engineering consultancy through our mandatory Customer Success Program (CSP).
Start your journey today.
Join the next wave of AI Agent. Scale your interaction analysis capacity with surgical precision.